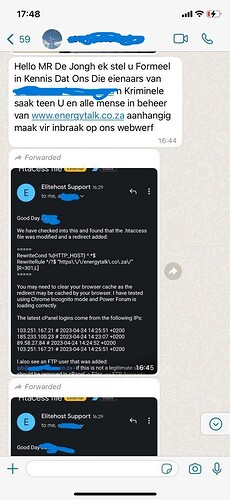
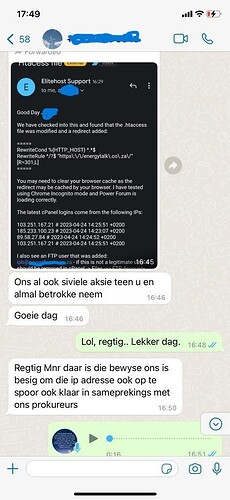
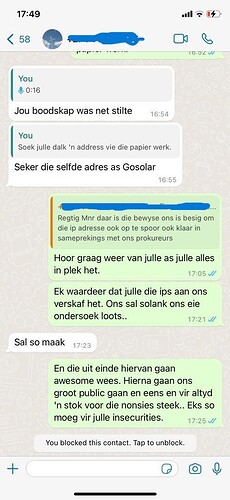
Right. So this most likely really happened. We have log files, and the log files confirm that around that time (14:31) we started getting traffic that was referred from that other site.
The short version of this: Over about a 3 hour period, we got roughly 95 hits this way. That is NOTHING compared to the normal traffic we get, and I’m certain it is also nothing compared to the traffic the other site gets in the same time frame. That redirect could not have been in place more than a few minutes, and the only reason it persisted for 3 hours is because the idiot who put the redirect in accidentally made it permanent. I’ll explain more below.
Let’s analyse for a moment what happened. From the above screenshots, we can see that a permanent redirect (301) was added to the .htaccess file. This is an apache configuration file. I remember it, but I haven’t used apache in about a decade. All the cool kids use nginx these days. The config line is this:
RewriteCond %{HTTP_HOST} ^.*$
RewriteRule ^/?$ "https\:\/\/energytalk\.co\.za\/" [R=301,L]
Alright, so what that does is it permanently (that is what the 301 means) redirects all traffic that is specificall on the root of the site (the / URL) to ours. If you were to access a page directly, it would not redirect.
Now there is a reason I emphasis that this redirect was permanent. What this means, is that a browser will remember it for a certain time period, until you clear the cache. If you want the redirect to be temporary, you would use a 302. Hence my comment above about the intelligence of this.
Now, browsers do an interesting thing. They put the site that referred them to the new URL in the Referer: header. The spec doesn’t say that browsers must do this, but most of them do (as long as you redirect from https to https, which is almost certainly the case here).
We can see the referrer on our side. So we can see how much traffic came our way because of this redirect. Also, we need to look specifically for requests going to the root of the site, a GET / request. There are 95 of them. Only 95. They come from around 36 different IP addresses. We’ve got those IP addresses. We can look up which provider owns those IPs. I can see the User Agent header, so I know what browsers are used.
Furthermore, the IP addresses in the email from their service provider is in Europe. 2 is in the UK, 1 is in France, and 1 is in Germany. Of course, whoever did this likely used a VPN.
So, my verdict.
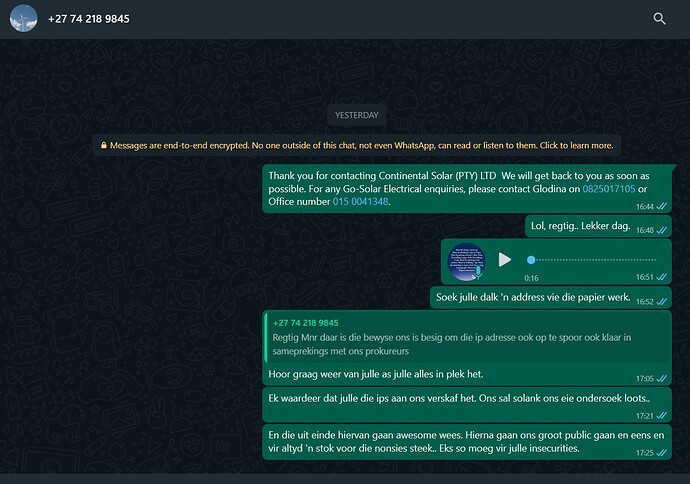
I do not believe for one second that this redirect was in place for more than a few minutes, based on the measly amount of traffic that was redirected. That makes it exceedingly likely that whoever did it, likely did it specifically for the purposes of starting a smear campaign.
I’ve kept a copy of the logs in a secure place. Just in case.
We (the guys admining this site) had nothing to do with this. We’re far too busy, and not nearly stupid enough to be this obvious about it.